Remote device management: A guide to free software & strategy
 GroWrk Team
GroWrk Team
Every laptop and mobile device outside your office offers a chance to save on resources, but also comes with a security risk. A lot can go wrong, like your employee losing the device or accidentally clicking on a malware link. But if you have a reliable remote device management (RDM) system in place, you can secure your data promptly without any risk.
Let’s explore why remote device management is essential, how to build a simple strategy, and which free RDM tools for 2026 can help your business stay secure and efficient without stretching your IT budget.
What is remote device management?
.jpg?width=600&height=300&name=remote%20device%20management%20(1).jpg)
Remote device management refers to the process of monitoring, controlling, and securing company-owned endpoint devices such as laptops, desktops, mobile phones, tablets, and IoT devices using remote device management software from a centralized location.
With RDM, your IT teams can:
-
Enforce password and encryption policies
-
Deploy or uninstall software remotely
-
Lock or wipe lost devices
-
Track asset inventory
-
Troubleshoot user issues in real time
In short, RDM gives businesses the control over their device and data security they once had inside the office, no matter where their people are.
Understanding remote device allocation models
Companies use different models to allocate devices to their distributed teams. The choice of allocation model directly impacts device users and their permissions, determining how access rights and security roles are managed for each user. Before jumping to the details, let’s take a quick glance at these models:
BYOD (Bring Your Own Device)
Employees work on their personal devices, such as a personal computer. This maximizes flexibility and often improves morale, but introduces security vulnerabilities and complicates IT management across diverse platforms and operating systems. Additionally, BYOD can expose organizations to potential security risks, making it essential to implement robust security measures.
CYOD (Choose Your Own Device)
Workers select from a curated list of company-approved devices, with options chosen based on operating system to ensure compatibility and effective remote device management. This strikes a middle ground, giving employees autonomy while maintaining IT standards and security protocols. CYOD also simplifies remote configuration management, making it easier for IT teams to deploy, update, and maintain devices consistently across the organization.
COPE (Corporate-Owned, Personally Enabled)
The company supplies corporate-owned devices that employees can use for both professional and personal activities. This delivers strong security oversight while respecting personal usage needs. Additionally, COPE enables better asset management by allowing organizations to efficiently configure, secure, and monitor devices remotely.
COBO (Corporate-Owned, Business Only)
Organizations provide work-exclusive devices with no personal use permitted. This offers maximum control, security, and privacy implications, ideal for highly regulated industries or sensitive data environments, such as when managing security systems that require strict oversight.
Why remote device management is a security imperative
.jpg?width=600&height=300&name=remote%20device%20management%20(4).jpg)
A recent study shows that about 60% of organizations experience cybersecurity breaches due to vulnerabilities in their remote work systems. Another report reveals that 78% of employees use BYOD, despite prohibitions, with unmanaged devices being the cause of over 90% of ransomware attacks.
Multiple devices with less security can lead to security breaches, making it critical to have robust remote device management in place. Managing and protecting these devices is no longer optional; it’s a core business function to protect both data and IT equipment. Here is why RDM is a security imperative for your business:
1. Protecting company data
When an employee loses a laptop on a business trip, the device might be gone, but your data doesn’t have to be. Remote management tools enable instant lock and remote wipe features, minimizing exposure of sensitive files or credentials. Additionally, regularly applying security patches is crucial to protect company data, as these updates address vulnerabilities and help prevent unauthorized remote access.
2. Enforcing security policies
Without physical oversight, you can’t rely on good intentions alone. Studies show that 85% of cybersecurity breaches involve a human element. Remote device management tools ensure every device follows baseline security standards, such as disk encryption, password complexity, and automatic screen locks, to reduce human error.
3. Ensuring software and OS are up-to-date
Outdated systems are a top attack vector. Centralized patch management allows you to deploy updates company-wide from one place, keeping everyone on the same security baseline. Remote device configuration further enables efficient updates by allowing IT teams to control, monitor, and troubleshoot devices from a distance through centralized platforms.
4. Enabling compliance and continuity
Whether it’s GDPR, SOC2, or HIPAA, compliance requires control over data access. RDM tools provide audit logs and policy enforcement, helping you meet your obligations with confidence. Automated compliance checks and equipment security agreements further reduce manual intervention, streamlining processes and ensuring consistent adherence to regulatory standards.
5. Remote troubleshooting
If your employees encounter any technical issues, remote device management solutions enable your IT team to troubleshoot problems quickly and efficiently, including troubleshooting devices remotely, without needing physical access. For a complete overview of providing laptops to remote employees, refer to this guide.
This ensures minimal downtime and keeps your remote workforce productive and supported, as remote access is essential for effective troubleshooting.
The core pillars of a remote device management strategy
.jpg?width=600&height=300&name=remote%20device%20management%20(3).jpg)
A strong RDM framework works on five strategic pillars:
-
Security policy design: Create clear, enforceable rules defining what users can access, how devices authenticate, and what data can be stored locally.
-
Visibility and automation: Automate device enrollment, update schedules, and compliance checks. Dashboards should show real-time device health and security status.
-
Access control and identity management: Integrate Single Sign-On (SSO) and Multi-Factor Authentication (MFA) to ensure only authorized users access corporate apps.
-
Data protection and compliance: Encrypt sensitive data and maintain detailed audit trails to support regulatory requirements.
-
Employee onboarding and offboarding: Ensure smooth device setup for new hires and secure deprovisioning during exits, preventing unauthorized access after departure.
Remote work security checklistBefore deploying any RDM tool, make sure these essentials are in place:
Pro tip: Turn this checklist into a recurring audit task for your IT or operations team. |
What are the 10 best free remote device management solutions for 2026?
Maintaining the security of your distributed devices and your company data on a budget is hard, but not impossible. We understand the challenges of remote work and have done the research to find real, free solutions that solve major security and efficiency problems. Here is a quick overview of our top RDM picks for 2026 to help you manage remote workers' devices:
|
Tool |
Best for |
Free plan limit |
Platforms |
Security rating |
|
|---|---|---|---|---|---|
|
GroWrk |
Remote teams & hybrid workforce |
Free trial for all features |
Windows, macOS, Linux, iOS |
5/5 |
|
|
ManageEngine MDM Plus |
Comprehensive management |
25 devices |
Android devices, iOS, Windows, macOS |
5/5 |
|
|
Jamf Now |
Apple ecosystems |
3 devices |
macOS, iOS |
4/5 |
|
|
Comodo MDM |
Security-focused businesses |
Free |
Android, iOS, Windows |
5/5 |
|
|
Microsoft Intune |
Microsoft 365 users |
30-day trial |
All major OS |
5/5 |
|
|
SureMDM |
Versatility & cross-platform support |
Free |
Windows, Android devices, iOS |
4/5 |
|
|
Zoho MDM Plus |
SMBs needing BYOD control |
25 devices |
Cross-platform |
4/5 |
|
|
Google Endpoint Management |
Workspace users |
Free |
All major OS |
4/5 |
|
Now, let’s discuss each free remote device management solution individually, what they are best for, the top feature in the free plan, pros & cons, and the pricing plans.
1) GroWrk

GroWrk is built for distributed companies and offers a smooth onboarding and device lifecycle management experience. IT managers can configure and ship pre-secured laptops globally, track device compliance, and enforce policies remotely; all from a centralized dashboard that serves as a centralized location for managing devices.
Key Features:
-
Full remote IT lifecycle management from deployment to disposal
-
Global reach in across 150+ countries to deploy, retrieve, store, and dispose of equipment
-
Automated zero-touch deployment and onboarding for remote employees
-
Manage application and data access remotely - lock, wipe, and recovery
-
Single sign-on (SSO) for MacOS, Windows, or Linux
-
Policy enforcement for security and compliance
-
Unified dashboard for all active devices and seamless integration with existing systems
-
Identity management for added security
-
Monitor device performance to ensure device health and quickly identify issues
Price: Free trial available. A la carte pay-as-you-go option, so you only pay for what you use.
Pros: Seamless for remote operations | Great UX | Strong global support
Cons: Requires you to pay a small one-time fee for
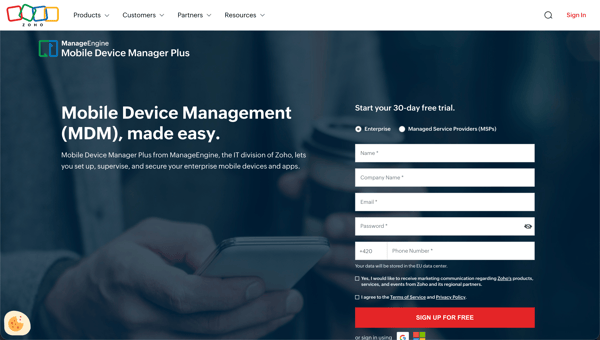
2. ManageEngine Mobile Device Manager Plus
ManageEngine MDM Plus combines mobile and desktop management into one unified endpoint management solution. As a comprehensive mobile device management (MDM) platform, it’s ideal for organizations managing mobile devices, laptops, and other IT equipment.
Key Features:
-
Free for up to 25 devices
-
Works on Android, iOS, Windows, macOS, and Chrome OS
-
Remote control, app management, and asset tracking
-
Patch tablet mobile device management for secure and efficient configuration, deployment, and monitoring software capabilities
Price: Free for 25 devices
Pros: Enterprise-level control | Great for mixed environments
Cons: Slightly complex UI for non-technical users
3. Jamf Now
Jamf Now simplifies Apple device management for SMBs. With zero-touch configuration, even non-IT staff can secure Macs, iPads, and iPhones in minutes. It enables organizations to manage Apple endpoint devices efficiently, ensuring security and compliance across all hardware.
Key Features:
-
Free for 3 Apple devices
-
Zero-touch setup via Apple Business Manager
-
Lost Mode, remote lock, and wipe
-
Custom app and configuration deployment
-
Password and encryption enforcement
-
Track and manage enrolled devices to maintain compliance
Price: Free for 3 devices
Pros: Native Apple integration | Perfect for small Apple-first teams
Cons: Apple-only support
4. Comodo MDM
Comodo MDM is renowned for security-first management, featuring real-time malware detection and device-level encryption. It suits finance, healthcare, and compliance-heavy industries.
Key Features:
-
Advanced encryption protocols
-
Real-time malware and threat detection
-
Conditional access and compliance policies
-
Remote lock and selective wipe
-
Advanced security features such as authentication protocols and security audits
-
Automatic deployment of security patches to protect against vulnerabilities
Price: Free
Pros: Industry-grade protection | Integrated compliance tools
Cons: Learning curve for first-time users
5. Microsoft Intune
Microsoft Intune provides a unified management layer across Microsoft services, combining device management with access control and endpoint analytics. With Intune, organizations can efficiently manage a wide range of devices, including desktop computers and any personal computer used by employees, ensuring secure and scalable remote device management.
Key Features:
-
Seamless integration with Office 365 and Defender
-
Remote lock, restart, and wipe
-
Endpoint analytics and compliance scoring
Price: Free trial (30 days)
Pros: Enterprise-ready | Perfect for existing Microsoft users
Cons: Setup complexity for smaller teams
6. Zoho MDM Plus
Zoho MDM Plus is a privacy-conscious platform that allows secure management of both corporate and personal devices, offering enterprise-grade features at zero cost for small teams.
Key Features:
-
25 devices free
-
Separate corporate container for BYOD
-
Remote lock, wipe, and geofencing
-
Manage device users and set permissions for each user
-
Control who can access devices remotely for troubleshooting and support
Price: Free for 25 devices
Pros: Great BYOD support | Feature-rich for SMBs
Cons: Slightly heavier interface. For a comparison of other options, check out our list of the best free device management software.
7. Google Endpoint Management
Google Endpoint Management is ideal for businesses that run on Google Workspace. This tool provides built-in control over all connected devices, including internet-connected devices and smart devices, without extra cost.
Key Features:
-
Auto-enrollment via Workspace login
-
Remote wipe and password enforcement
-
Basic app and access management
-
Context-aware access rules
-
Device activity and compliance reports
Price: Included free with Workspace
Pros: Simple setup | Seamless Workspace integration
Cons: Limited to basic policies
How to set up your remote device management tools in 5 simple steps?
Step 1: Assess Your Device Landscape
Catalog every endpoint: laptops, desktops, mobile devices, tablets, endpoint devices, and IoT devices. Note the operating systems and ownership models (corporate vs. BYOD).
Step 2: Choose Your Tool
Pick one of the free remote device management tool options above and test its dashboard functionality. Look for real-time visibility, remote commands, reporting, and the ability to monitor device performance.
Step 3: Define Core Security Policies
Decide what “secure” means for your business; e.g., addressing security threats in your policies, encryption required, password length, or no public Wi-Fi use. Establish minimum standards:
-
Enforce full-disk encryption
-
Require MFA for all logins
-
Limit admin rights to IT staff
-
Enforce VPN usage
-
Enable auto-lock after inactivity
-
Implement security features such as authentication protocols and regular security audits
Step 5: Enroll Devices
Use bulk enrollment via email links or QR codes to add enrolled devices to your system. Ensure each new device joins your RDM environment during setup, minimizing manual intervention during enrollment.
Step 6: Test Remote Actions
Try locking a test device, sending a message, triggering a software update, or attempting to control devices remotely to confirm everything works as intended. Also, test monitoring performance features to ensure you can oversee system health and efficiency.
What to expect when you outgrow a remote device management platform free plan?
.jpg?width=600&height=300&name=remote%20device%20management%20(5).jpg)
Free plans are a great starting point, but as your team and device fleet grow, you’ll hit limitations. When device sprawl or security needs surpass the capabilities of your free plan, it’s time to consider upgrading to a solution that can grow with your business. Here’s what you can expect when it’s time to upgrade, including the impact on operational cost:
Support for More Than 25 Devices
Most free RMD tool plans typically limit the number of devices to a maximum of 25. As your company grows, managing more enrolled devices and endpoint devices becomes difficult without the scalability of a paid plan.
Access to 24/7 Support and SLAs
Paid plans often include access to a dedicated technical support team, round-the-clock support, and custom Service Level Agreements (SLAs), ensuring faster response times and guaranteed uptime when selecting MDM solutions for Apple devices.
Advanced Features for Automation and Analytics
Upgrading unlocks more advanced features, such as the ability to monitor device performance, configuration management, automated software deployment, detailed device health reporting, and powerful compliance tracking; all essential for managing large, distributed teams efficiently.
Cross-Department Integrations
As you scale, integrating your RDM solution with other business tools (like HR systems or SIEM tools), as well as asset management platforms and solutions to access devices remotely, becomes crucial for smooth operations and better visibility.
Enhanced Security and Compliance
Free plans may offer basic security, but paid versions provide robust security features, advanced protection against security threats, and tools to help prevent data breaches, along with comprehensive compliance tools for meeting industry standards (ISO, SOC 2, HIPAA), ensuring that sensitive data remains protected.
Why businesses choose GroWrk for remote device management
-
End-to-end lifecycle: Procure, configure, deploy, manage, recover, and securely dispose of devices from one platform.
-
Global at scale: Operate in 150+ countries with local logistics, customs handling, and compliant returns.
-
Zero-touch onboarding: Automate setup and policy enforcement so new hires are productive on day one.
-
Unified RDM + MDM: Enroll into your MDM, push configs/apps, enforce security (lock/wipe), and track compliance centrally.
-
Identity-first security: Built-in SSO/MFA integrations and role-based access to protect accounts and data.
-
Real-time visibility: Live asset inventory, device health, and audit trails for governance and reporting.
-
AI-assisted ops: GroWbot helps with 24/7 triage, policy checks, and common device issues to reduce IT workload.
-
Open ecosystem: Integrations with HRIS, ITSM, SIEM, finance/ERP, and collaboration tools to sync workflows.
-
Transparent pricing: Straightforward per-workstation model, no opaque tiers or surprise add-ons.
-
Sustainability built-in: Certified data wiping, reuse/redeployment options, and documented e-waste recycling.
-
Enterprise-grade support: Dedicated CSMs, global coverage, and SLA-backed assistance for distributed teams.
GroWrk combines global reach, secure automation, and clear pricing to make remote device management simple, compliant, and scalable. Request a demo now to keep your remote IT devices secure.
FAQs
Can I manage employees' personal devices (BYOD)?
Yes. Modern RDM tools support containerization. In this approach, corporate data is isolated from personal apps, ensuring employee privacy and organizational control.
What is the difference between RDM vs. RMM vs. MDM?
RDM (Remote Device Management) is sometimes confused with MDM (Mobile Device Management) or RMM (Remote Monitoring and Management). The distinction lies in focus:
-
MDM primarily focuses on smartphones and tablets.
-
RMM is used by MSPs to manage client networks and servers.
-
RDM combines elements of both, covering mobile and desktop environments in distributed workforces.
How difficult is it to enroll a remote employee's new laptop?
It is an easy task to enroll a remote employee's new laptop. Most free tools offer automatic no-touch enrollment via email or QR code, taking under 30 minutes to configure.
Can RDM be used to manage devices in multiple geographical regions?
Yes, RDM platforms often have global reach, allowing companies to manage devices and enforce security policies across different time zones and geographic locations. This means you can conveniently manage devices from any remote location, whether it's a company office, your home workspace, or even while traveling.
How can RDM tools help reduce IT operational costs?
RDM tools automate routine tasks like software updates, security enforcement, and device monitoring, freeing up IT resources and minimizing manual oversight, thus reducing operational costs.
What happens if an employee leaves the company? How is their device managed?
With RDM, IT administrators can securely deprovision devices of former employees, remotely wiping all corporate data, ensuring that sensitive information is no longer accessible. Additionally, a remote factory reset can be used to restore devices to their original factory settings, providing an extra layer of security and making devices ready for reuse or reconfiguration.
Can RDM tools integrate with other IT management systems?
Yes! Many RDM solutions like GroWrk offer API integrations with your existing systems and HR platforms to streamline device management, user provisioning, and ticketing systems. Integration with POS systems is also supported, allowing for centralized management, monitoring, and troubleshooting of these devices remotely.






